Research | Why implement an Intrusion Detection System (IDS) into a WordPress website?
What is an Intrusion Detection System (IDS) and what does it do? How it works? And why you need it for your website? What metodology and best practices? An Intrusion Detection System (IDS) can alert you to a security breach or intrusion as soon as it occurs, giving you time to take action to prevent further damage.
What is an Intrusion Detection System (IDS) and what does it do?
As the popularity of WordPress as a content management system (CMS) grows each year, the need to secure the WP platform has become a priority.
WordPress is a target for attacks due to the large number of WordPress websites – it is the most popular CMS, which logically attracts the most attention from hackers.
We all know that an important part of any CMS is security, WordPress sites included. Achieving this is not always easy, and WordPress sites are vulnerable to many attacks.
Intrusion Detection Systems (IDS) can help alleviate these concerns, as an important part of any security strategy, they can alert you to signs of attacks. IDS can often be the first defense against a potential attack, while also providing a way to monitor your security.
How do Intrusion Detection Systems (IDS) work?
This type of systems works by monitoring the network or systems for strange activity, such as a user logging into the network from an unknown location or an employee accessing files from home under unusual circumstances. An Intrusion Detection System consists of 2 main components:
- 1. sensors, which consist of physical devices such as cameras and sensors or, in the case of WordPress, plugins.
- 2. analyzers, that identify the strange actions and alert the administrator(s).
In this way, organizations and individuals can ensure that their systems are protected from unauthorized access, data breaches, data loss, and malicious attacks. A small portion of the functionality of IDS is performed by humans, but the majority is automated. The process of reviewing alerts generated by an IDS is called intrusion detection.
The most important rule to remember about IDS is that it is a tool. You need to deploy it and then interpret the results. A properly deployed IDS can be a good defense, but it is no substitute for a properly secured WordPress website.
The benefits of an intrusion detection system in WordPress are many. One way to experience the benefits is to think of the WordPress dashboard as a castle: every time you log into the dashboard, you enter the castle, and you want to know that the castle is secure and that you can enter and leave without fear of intruders.
The reason intrusion detection is so important on a WordPress site is because WordPress sites are essentially a database running a scripting language. It is the scripting language that can be vulnerable to attacks and exploits, especially if you are running a site on a shared server.
Classification of Network Intrusion Detection System (NIDS) based on IDS
NIDS is a type of network based on Intrusion Detection System. It is used to detect unauthorized activity on a computer network and generate an alert. It can detect many types of attacks, such as unauthorized access, misuse of an application, virus or worm activity, and denial-of-service attacks. A NIDS is essentially a combination of an intrusion prevention system (IPS) and a firewall, deployed at the network layer rather than the host layer. In other words, a NIDS protects a network or part of a network from network-level attacks.
- HIDS – Host Intrusion Detection System. HIDS is a type of program that monitors your server for suspicious behavior. When it detects something, it lets you know. Typically, a HIDS monitors the server logs (99.99% of what is logged in the security log is blocked hackers, spammers, bad bots, scrapers, miners, etc.). This is because the most popular way to hack a website is through a SQL injection attack, and most of these attacks are through the website database. HIDS looks for unauthorized commands in the logs and alerts you when something has been executed.
- Log-based Intrusion Detection System (PIDS). PIDS monitors suspicious traffic on the network and analyzes non-standard use of network protocols (protocols) such as TCP and UDP.
- Application Protocol-based Intrusion Detection System (APIDS). APIDS is a similar system to Intrusion Detection System (IDS), but uses application layer services instead of network layer services. APIDS can detect attacks that previously went undetected by IDS.
- Hybrid Intrusion Detection System. A hybrid intrusion detection system is a form of IDS that combines the capabilities of NIDS and HIDS. While NIDS and HIDS differ in the way they are configured and deployed, they both have the same general purpose, which is to detect and stop an attack on a network.
Types of IDS methodologies
The two main forms of IDS techniques are:
- 1. network monitoring (proactive)
- 2. scanning (reactive)
When used properly, network monitoring and scanning can provide you with 24/7 protection that alerts you to abnormal network activity or identifies a system breach.
Signature-Based IDS
A signature-based IDS works to stop system hacking attempts by unauthorized users by identifying specific malicious attacks and patterns of attacks or access attempts. The system is based on the idea that each attack has its own unique characteristics. By creating a list of malicious patterns, the system can identify an attack before it has a chance to do any damage. This list of patterns is called a “signature.” The signature-based IDS software analyzes each event and makes a comparison between the signature list and events. If the event matches a signature, the system takes an action. However, if the event does not correspond a signature, the system takes no action.
Anomaly-Based IDS
Anomaly-based IDS, also known as statistical IDS or behavior-based IDS, is an IDS type that generates an alert based on a statistical threshold for a measure of normal behavior.
Normal behavior is typically the baseline traffic for the system that the IDS is protecting against. Anomalies are defined as any traffic that does not correspond the baseline.
Anomaly-based IDSs are similar to misuse-based IDSs that detect attacks based on a known signature, which is a list of known attacks.
Challenges in managing an Intrusion Detection System
Identifying or protecting against cyber threats is a never-ending battle. Even if a company has the best security in place from the start, it can be a losing battle if it is not constantly on guard. A simple hack can ruin a company’s reputation and revenue, so having an IDS is a must for any business. But monitoring an IDS is hard work. And there’s always the risk of hackers figuring out how to hack the system, or making off with your data in the first place.
Intrusion Detection Systems are an important part of a comprehensive security program. However, they are not foolproof, as they rely largely on correlation and statistical analysis. They rely on collecting data and analyzing it for irregularities, which is not possible with all types of tools, including those running on a cloud-based platform. Therefore, it is important to establish a baseline of usage and take immediate action when an intrusion is detected.
While it’s important to keep a close eye on IDS logs for signs of attack or suspicious activity, it’s important that you don’t become so overwhelmed by the flood of alerts that you can no longer distinguish the critical (real risks) from the mundane (false positives).
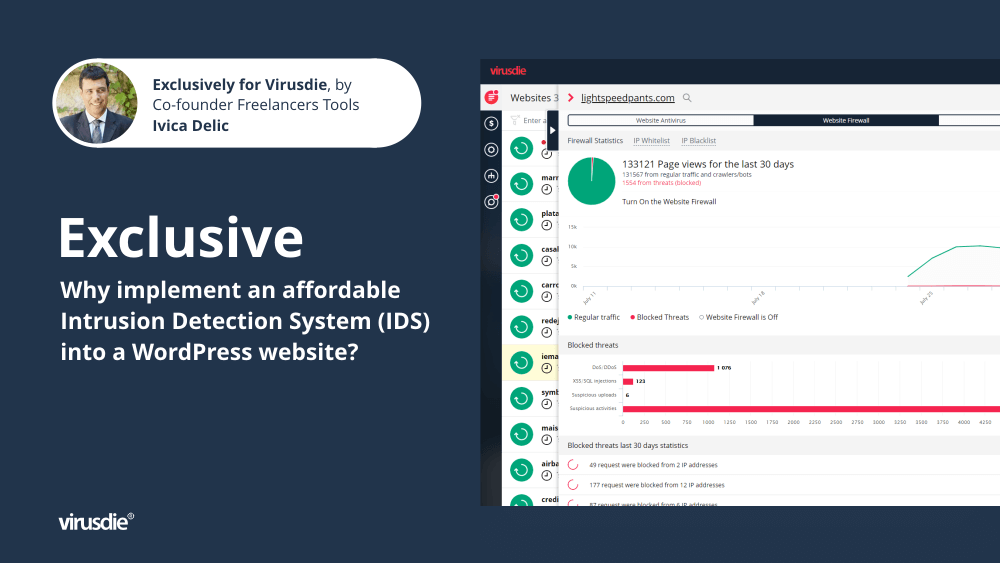
The best Intrusion Detection System plugins in WordPress
To minimize the damage a hacker can do to a WordPress site, many WordPress site owners turn to Intrusion Detection System (IDS) WordPress plugins that help protect sites and users, to list just a few in random order (some of which we’ve tested in in real-world situations, on some of the sites we run):
What is an Intrusion Prevention Systems (IPS)?
Intrusion Prevention System (IPS) is an active security system that monitors network or host traffic for malicious activity or policy violations. An IPS is created to detect and prevent unauthorized access or activity by identifying suspicious patterns and blocking malicious traffic. Unlike IDS, IPS has the ability to block unwanted traffic. Therefore, an IPS security tool uses a number of technologies, including firewalls and antivirus software, to protect against unauthorized access.
Why using IDS and IPS together is Critical to Cybersecurity
Using IDS and Intrusion Prevention System (IPS) together is the smartest thing you can do for websites you maintain. An IDS can show you if a cyber intrusion attempt was successful, but IPS is needed because it stops the attack cold. IDS can only detect an intrusion attempt that has already occurred. Beyond that, IPS goes further by actually preventing the intrusion attempt. The fact that an attempted break-in has occurred can be crucial information. You can find out that a cybercriminal has already gained access to a network and is in the process of stealing data. The IDS alerts the network administrator, who then begins to contain the attack and try to limit the damage.
That’s why IDS and IPS were created, to detect and stop attacks on your network. When you combine these two security components, you get a system that not only stops attacks, but also prevents damage.
—
However, we must all need be aware that there is no 100% complete solution that can protect every environment.
—
Article by Ivica Delic
founder of FreelancersTools,
exclusively for Virusdie.
Join our private Facebook group to get help from other security experts, and share your own web security experiences and expertise. Group members receive exclusive news and offers. They can also communicate directly with the Virusdie team. Join us on Facebook.

Comments